Things about Risk Management Enterprise
Table of ContentsGetting The Risk Management Enterprise To WorkWhat Does Risk Management Enterprise Do?Facts About Risk Management Enterprise UncoveredRisk Management Enterprise Fundamentals ExplainedTop Guidelines Of Risk Management EnterpriseThe Of Risk Management EnterpriseRisk Management Enterprise Fundamentals Explained
Below are several of its key features that centers have to recognize. Take a look. Real-Time Danger Analyses and Reduction in this software program enable organizations to constantly keep an eye on and examine risks as they develop. This function leverages real-time data and automated evaluation to determine potential dangers promptly. Once risks are identified, the software facilitates immediate reduction actions.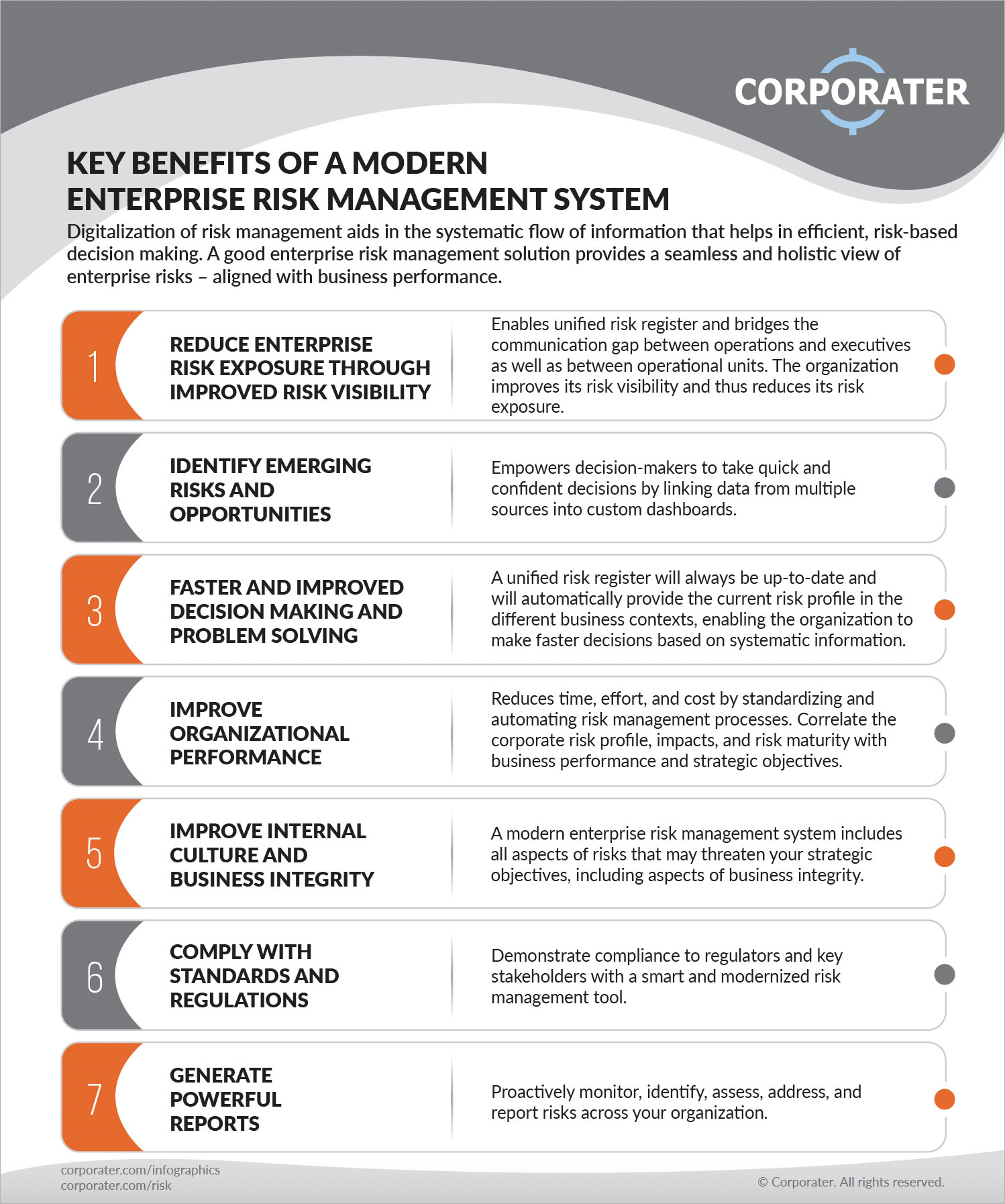
KRIs fix the issue of irregular or uncertain risk analysis. They attend to the obstacle of continuous risk monitoring by offering tools to keep an eye on risks continually. KRIs enhance safety and security danger oversight, guaranteeing that possible dangers are determined and managed successfully. The task of threat monitoring ought to not be an obstacle. Organizations have to rely on a superior and sophisticated risk monitoring software application.
Risk Management Enterprise Fundamentals Explained
IT risk management is a part of business danger management (ERM), developed to bring IT take the chance of in accordance with a company's danger cravings. IT take the chance of monitoring (ITRM) includes the policies, procedures and technology essential to lower dangers and susceptabilities, while keeping compliance with appropriate regulatory requirements. On top of that, ITRM looks for to limit the consequences of damaging events, such as security violations.
While ITRM frameworks give helpful guidance, it's simple for IT teams to deal with "framework overload." Veronica Rose, ISACA board supervisor and an info systems auditor at Metropol Corp. Ltd., suggests the usage of a combination of structures to achieve the ideal results. The ISACA Danger IT framework lines up well with the COBIT 2019 structure, Rose stated.
Business Threat Administration Software Advancement: Conveniences & Characteristics, Expense. With technological innovations, risks are constantly rising. That being said, companies are more probable to deal with obstacles that impact their financial resources, operations, and online reputation. From rapidly changing markets to regulatory modifications and cyber hazards, companies navigate with a frequently changing sea of risks.
5 Easy Facts About Risk Management Enterprise Shown
In this blog site, we will study the globe of ERM software program, discovering what it is, its benefits, attributes, etc to ensure that you can build one for your business. Venture Threat Administration (ERM) software is the application program for preparation, routing, arranging, and managing business activities and improving threat administration procedures.
With ERM, organizations can make informative choices to improve the overall resilience of the service. Committed ERM systems are essential for services that consistently deal with large amounts of delicate details and several stakeholders to accept strategic decisions.
It can be stayed clear of by utilizing the ERM software application system. This system automates guideline compliance administration to keep the organization protected and compliant.
Not known Facts About Risk Management Enterprise
You can also attach existing software application systems to the ERM using APIs or by including information manually. Services can utilize ERM to evaluate dangers based on their prospective effect for better danger monitoring and mitigation.: Adding this function permits individuals to obtain real-time notifications on their tools regarding any kind of threat that could happen and its influence.

Instead, the software permits them to set limits for various procedures and send press notices in situation of possible threats.: By incorporating data visualization and reporting in the customized ERM software application, companies can gain clear understandings about risk fads and performance.: It is required for organizations to stick to sector conformity and regulatory requirements.
These platforms make it possible for firms to carry out best-practice threat monitoring processes that line up with sector standards, supplying a powerful, technology-driven strategy to identifying, examining, and mitigating threats. This blog site discovers the benefits of automated threat monitoring devices, the areas of risk management they can automate, and the worth go to website they bring to an organization.
An Unbiased View of Risk Management Enterprise
Teams can set up kinds with the appropriate areas and quickly develop different kinds for different risk kinds. These risk analysis types can be flowed for completion using automated operations that send out notifications to the appropriate personnel to finish the types online. If kinds are not finished by the due date, after that chaser emails are immediately sent out by the system.
The control surveillance and control testing procedure can also be automated. Companies can use computerized process to send regular control test alerts and personnel can get in the results by means of online forms. Controls can also be checked by the software by setting policies to send out signals based on control data kept in various other systems and spread sheets that is drawn right into the platform through API assimilations.
Threat administration automation software program can also support with danger coverage for all levels of the enterprise. Leaders can check out records on threat exposure and control efficiency via a selection of reporting outputs including fixed records, Power BI interactive records, bowtie evaluation, and Monte Carlo simulations. The capacity to draw genuine time records at the touch of a switch removes strenuous information control tasks leaving danger teams with even more time to examine the information and advise the company on the most effective program of action.
Organizations operating in affordable, fast-changing markets can not pay for delays or inefficiencies in addressing possible risks. Typical threat administration using hand-operated spreadsheet-based procedures, while acquainted, commonly lead to fragmented data, lengthy coverage, and an enhanced likelihood of human mistake.
The 2-Minute Rule for Risk Management Enterprise
This makes certain threat registers are constantly current and lined up with business goals. Compliance is one more essential chauffeur for automating danger management. Criteria like ISO 31000, CPS 230 and COSO all give support around threat management best techniques and control frameworks, and automated danger monitoring tools are structured to line up with these demands aiding companies to meet most commonly utilized danger monitoring criteria.
Look for risk software platforms with an authorizations power structure to easily set up workflows for risk acceleration. This performance enables you to tailor the sight for every individual, so they just see the information appropriate to them. Ensure the ERM software application uses individual monitoring so you can see who entered what information and when.
Choose a cloud-based system to make certain the system receives routine updates from the vendor adding new functionality. Seek tools that offer project threat monitoring abilities to manage your projects and portfolios and the linked threats. The benefits of taking on danger administration automation software application extend far beyond performance. Organizations that incorporate these services into their ERM strategy can anticipate a host of substantial and intangible.

The 5-Minute Rule for Risk Management Enterprise
While the instance for automation is compelling, carrying out a risk management system is not without its challenges. For one, information high quality is vital. Automated systems count on exact, updated information to provide significant understandings. To get rid of the challenges of danger management automation, companies should buy data cleaning and governance to make certain a solid structure for carrying out an automated system.
Automation in threat monitoring empowers services to change their approach to run the risk of and construct a stronger foundation for the future (Risk Management Enterprise). The inquiry is no longer whether to automate threat monitoring, it's how soon you can start. To see the Riskonnect in activity,
The answer commonly copyrights on how well dangers are prepared for and managed. Project administration software program offers as the navigator in the tumultuous waters of project implementation, offering devices that recognize and assess risks and design techniques to alleviate them properly. From real-time information analytics to comprehensive risk tracking control panels, these devices supply a 360-degree sight of the job landscape, making it possible for task supervisors to make enlightened choices that maintain their tasks on track and within budget.